OpenAI disclosed Wednesday that hackers compromised some employee devices through a code security vulnerability, though the company insists no user data or proprietary AI models were accessed. The breach, which OpenAI attributes to a supply chain attack, marks the latest security incident for the AI giant as it races to protect its crown jewels while scaling ChatGPT and GPT-4 to hundreds of millions of users. The incident raises fresh questions about enterprise security practices at AI companies handling sensitive training data and model weights worth billions.
OpenAI just confirmed what every AI company fears most - hackers got inside. The company disclosed that attackers compromised several employee devices through a code security vulnerability, though it's scrambling to reassure users and investors that the damage was contained.
According to OpenAI's statement reported by TechCrunch, the breach was "limited to the employees' devices" and didn't touch user data, production systems, or the company's closely guarded intellectual property - the AI models that power ChatGPT and are valued in the tens of billions. But the fact that hackers breached any part of OpenAI's infrastructure is sending ripples through the enterprise security community.
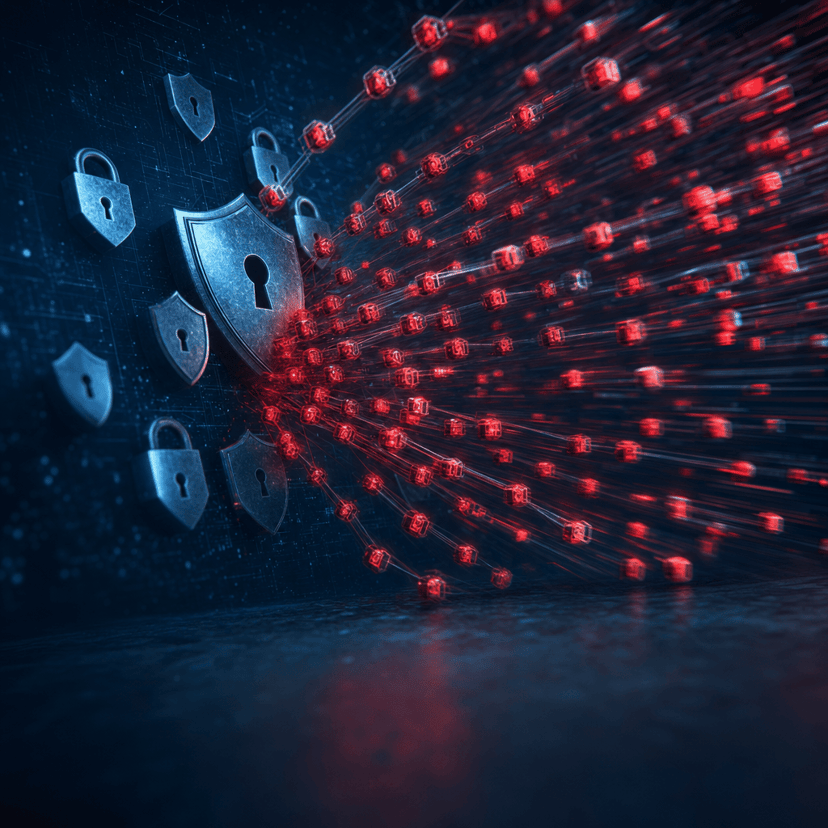
The attack vector appears to be a supply chain compromise, with security researchers linking it to a campaign known as TeamPCP that's been targeting technology companies through vulnerabilities in widely used development tools and open source packages. These supply chain attacks have become the nightmare scenario for tech companies - malicious code hidden in legitimate software libraries that developers unwittingly install on their machines.
For OpenAI, the timing couldn't be worse. The company is in the middle of a massive enterprise push, trying to convince Fortune 500 companies to trust it with their most sensitive data. Just last month, Microsoft - OpenAI's biggest investor and partner - reportedly expressed concerns about security practices during integration discussions. Now those concerns look prescient.
The breach follows a pattern we've seen across the AI industry. As these companies race to ship new models and features, security sometimes takes a backseat. Anthropic, Google's DeepMind, and other AI labs have all beefed up security teams in recent months, but the attackers are moving just as fast.
What makes this incident particularly concerning is the "code security issue" language. That suggests the vulnerability was in OpenAI's development pipeline - potentially in how engineers build, test, and deploy updates to ChatGPT and the company's API services. If hackers compromised developer machines, they could theoretically have planted backdoors or stolen credentials, even if they didn't get the model weights themselves.
OpenAI hasn't disclosed exactly how many employees were affected, what data was stolen from those devices, or how long the attackers had access before detection. Those details matter enormously. Employee devices often contain everything from internal communications to API keys to customer information shared via Slack or email.
The supply chain angle is especially troubling for the broader tech ecosystem. The TeamPCP campaign has been linked to compromises of popular npm packages and Python libraries - the exact tools that AI engineers rely on daily. If attackers can poison these wells, they can potentially reach dozens of companies through a single malicious package.
Security experts have been warning about this exact scenario. "AI companies are high-value targets with startup-speed security practices," one CISO at a major cloud provider told reporters last month. "They're moving so fast that basic security hygiene sometimes gets skipped."
OpenAI has been ramping up its security investments, hiring away talent from Meta, Google, and traditional cybersecurity firms. The company created a new security division earlier this year focused specifically on protecting its AI models from theft and ensuring its training pipeline can't be compromised. But defense is always harder than offense, especially when nation-state actors and sophisticated criminal groups are involved.
The incident will likely accelerate the broader conversation about AI security standards. Enterprise customers are already demanding more transparency about how AI companies protect their infrastructure. Expect to see new security certifications, third-party audits, and insurance requirements becoming standard in AI vendor contracts.
For now, OpenAI is in damage control mode, emphasizing that user data remained secure and its core AI systems weren't touched. But the breach is a stark reminder that even the world's most valuable AI company isn't immune to the same security challenges facing the rest of the industry.
This breach won't sink OpenAI, but it's a wake-up call for the entire AI industry. As these companies race to deploy increasingly powerful models to millions of users, security can't be an afterthought. Enterprise customers evaluating AI vendors should be asking harder questions about security practices, incident response protocols, and supply chain vetting. The fact that OpenAI contained this to employee devices is good news, but the next attack might not be so limited. For an industry that's reshaping how businesses operate, getting security right isn't optional - it's existential.