Artificial intelligence is now embedded in everything from recommendation engines to enterprise automation systems. Most of the headlines focus on generative AI and productivity gains. Less attention is given to what is happening inside enterprise infrastructure, where AI is quietly transforming how networks are defended.
At the same time, AI systems are creating entirely new network risks. Organizations are using AI to detect anomalies, automate responses, and reduce investigation time, while simultaneously deploying AI workloads that expand their own attack surface. The relationship works in both directions, and it is changing how security architecture is designed.
Why Traditional Network Defense Is Under Pressure
Enterprise networks no longer resemble the relatively predictable environments of the past. Cloud workloads shift dynamically. APIs connect services across providers. Remote users access systems from personal devices. IoT sensors and edge systems continuously stream data to centralized analytics platforms.
Static rule-based controls struggle in that environment. Traditional firewalls depend heavily on predefined signatures and manually configured policies. While those controls still matter, they are not sufficient when traffic patterns evolve constantly, and attackers automate reconnaissance and exploitation.
Security teams face an additional constraint. The volume of alerts continues to grow, and skilled analysts remain in short supply. In many organizations, cybersecurity retention becomes a real issue as experienced professionals move between roles or leave due to burnout pressure. AI-assisted monitoring has emerged partly as a response to that operational strain.
How AI Is Being Applied to Network Defense
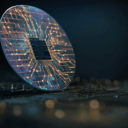
Machine learning models are well-suited to analyzing high-volume telemetry. Modern networks generate streams of logs, flow data, authentication attempts, and behavioral indicators. Instead of depending exclusively on known threat signatures, AI systems build baselines of normal behavior.
When deviations occur, the system can escalate alerts or apply automated controls. An internal account transferring data outside its usual window may trigger additional inspection. A device communicating with unfamiliar domains may be isolated. An unexpected spike in API traffic can be rate-limited before downstream systems are impacted.
This approach is commonly described as AI network security, where behavioral modeling augments traditional enforcement points. The objective is not to replace existing infrastructure but to enhance it with adaptive intelligence that adjusts as environments evolve.
AI Systems Introduce Their Own Risk
AI-driven applications rely heavily on network connectivity. Training pipelines pull data from storage systems. Inference endpoints serve predictions across distributed services. External APIs feed models with fresh data. Each connection must be evaluated carefully.
Misconfigured access controls or overly permissive routing rules can expose sensitive data or intellectual property. Model manipulation attacks and adversarial inputs further complicate matters. These threats often surface as unusual traffic patterns before they appear as application errors.
As organizations deploy AI more broadly, segmentation becomes essential. Systems handling training data should not be reachable from unrelated workloads. Inference services should be accessible only to authorized components. These controls depend on deliberate network architecture rather than assumptions of trust.
Governance and Risk Frameworks
Regulatory bodies and standards organizations have begun formalizing expectations around AI governance. Guidance such as the NIST AI Risk Management Framework emphasizes monitoring, logging, and clear accountability for AI systems. These recommendations assume strong visibility into data flow and system access.
You can see this reflected in detailed documentation on responsibly managing AI risks and aligning infrastructure with governance controls. Network-level enforcement becomes a foundational requirement for meeting those expectations.
Without consistent inspection and segmentation, enforcing policies around model access or training data integrity becomes significantly more difficult.
Automation at Scale
One of the key advantages AI brings to network defense is speed. Large enterprises process enormous volumes of traffic every second. Human analysts cannot review each anomaly individually.
AI-enabled systems can adjust policies dynamically. If abnormal authentication patterns suggest a credential compromise, access restrictions can be tightened automatically. If lateral movement is detected between workloads, segmentation policies can isolate affected systems quickly.
This reduces dwell time and limits potential impact before a manual investigation completes. It also helps offset staffing challenges in environments where security teams are stretched thin.
However, automation depends on reliable telemetry. If logging is incomplete or visibility gaps exist between cloud and on-premises systems, AI models operate with limited context. That reduces detection accuracy.
Cloud and Edge Complexity
AI workloads frequently operate across distributed environments. Edge devices collect raw data. Cloud platforms process and analyze it. APIs connect services across regions. Each connection introduces exposure that must be monitored.
Maintaining consistent enforcement across these layers requires coordination between virtual firewalls, cloud-native inspection tools, and centralized analytics systems. Policies should follow workloads across regions rather than remain tied to a single physical perimeter.
For teams building AI-driven applications, reviewing how traffic is segmented and inspected across infrastructure layers is critical. Many incidents arise not from model failure but from inconsistent enforcement between environments.
Organizations that adopt modern next-generation firewall architectures and integrate them with AI-driven monitoring tend to manage this complexity more effectively.
Collaboration Between Teams
AI engineering teams focus on model performance and deployment pipelines. Security teams focus on containment and compliance. As AI becomes embedded in production systems, these roles increasingly intersect.
If a model generates outbound API calls, network policies must account for those connections. If training pipelines ingest third-party data, its origin and integrity must be verified. Clear communication ensures that AI innovation aligns with security controls rather than bypassing them.
Security teams, in turn, benefit from understanding how AI workloads behave so policies reflect real usage rather than generic assumptions.
The Bigger Picture
AI is influencing both sides of the security equation. It strengthens detection and response capabilities while also expanding the systems that must be protected. Organizations cannot treat AI workloads as experimental projects detached from infrastructure planning.
The network remains the connective layer linking models, data sources, and users. Securing that layer requires adaptive enforcement, clear governance, and reliable visibility. As AI adoption accelerates, the resilience of that network foundation becomes increasingly important.
Smarter algorithms will continue to evolve. Ensuring they operate within well-designed and well-monitored networks will determine how safely they scale.